#Hack
Crypto news, in-depth analysis and latest market developments tagged Hack. The COINOTAG editorial desk keeps the latest 100 articles up to date.
20
5
June 2, 2026 at 03:42 AM UTC
A Hack in the cryptocurrency ecosystem refers to any unauthorized intrusion, exploit, or breach that compromises the security of a blockchain protocol, smart contract, centralized exchange, custodial wallet, or decentralized application, resulting in the theft, manipulation, or destruction of digital assets and the personally identifiable data of users. As the digital asset industry scales toward multi-trillion-dollar valuations, the frequency and sophistication of every Hack continues to escalate, with attackers leveraging cross-chain bridge weaknesses, oracle manipulation, reentrancy bugs, private-key compromise, governance takeovers, and increasingly AI-assisted social engineering to drain liquidity from protocols once considered battle-tested. The implications of a major Hack extend far beyond immediate financial loss: a single high-profile incident can trigger regulatory scrutiny, erode trust in DeFi primitives, slow institutional adoption of a spot Bitcoin or Ethereum ETF, and reshape the security expectations placed on validators, custodians, and Layer 2 sequencers. Within the broader ecosystem, the entanglement of AI & Crypto threat models, DeFi protocol design, and exchange custody architecture means that no participant—whether a retail holder relying on a cold wallet, a DAO treasury manager, or a centralized exchange operator—is fully insulated from the cascading effects of a meaningful breach. COINOTAG tracks every notable Hack with forensic clarity, documenting the on-chain trail, the affected counterparties, the disclosed root cause, and the remediation pathway, so readers can distinguish isolated implementation flaws from systemic vulnerabilities and adjust their personal risk posture accordingly. This dedicated section consolidates verified reporting, post-mortem analyses, white-hat disclosures, and stolen-fund recovery updates so that the lessons of each Hack translate into measurable improvements across the wallets, bridges, and contracts that custody the next cycle of capital.
Latest Articles
20 articles
Robinhood Completes $180M WonderFi Deal as Radiant Capital Winds Down After $50M Hack
Crypto News Robinhood Markets has officially closed its $180 million acquisition of Toronto-based digital asset firm WonderFi, marking the U.S. retail brokerage's formal entry into Canada's regulated crypto market. The deal, first announced in May 2025, brings WonderFi's two flagship pla
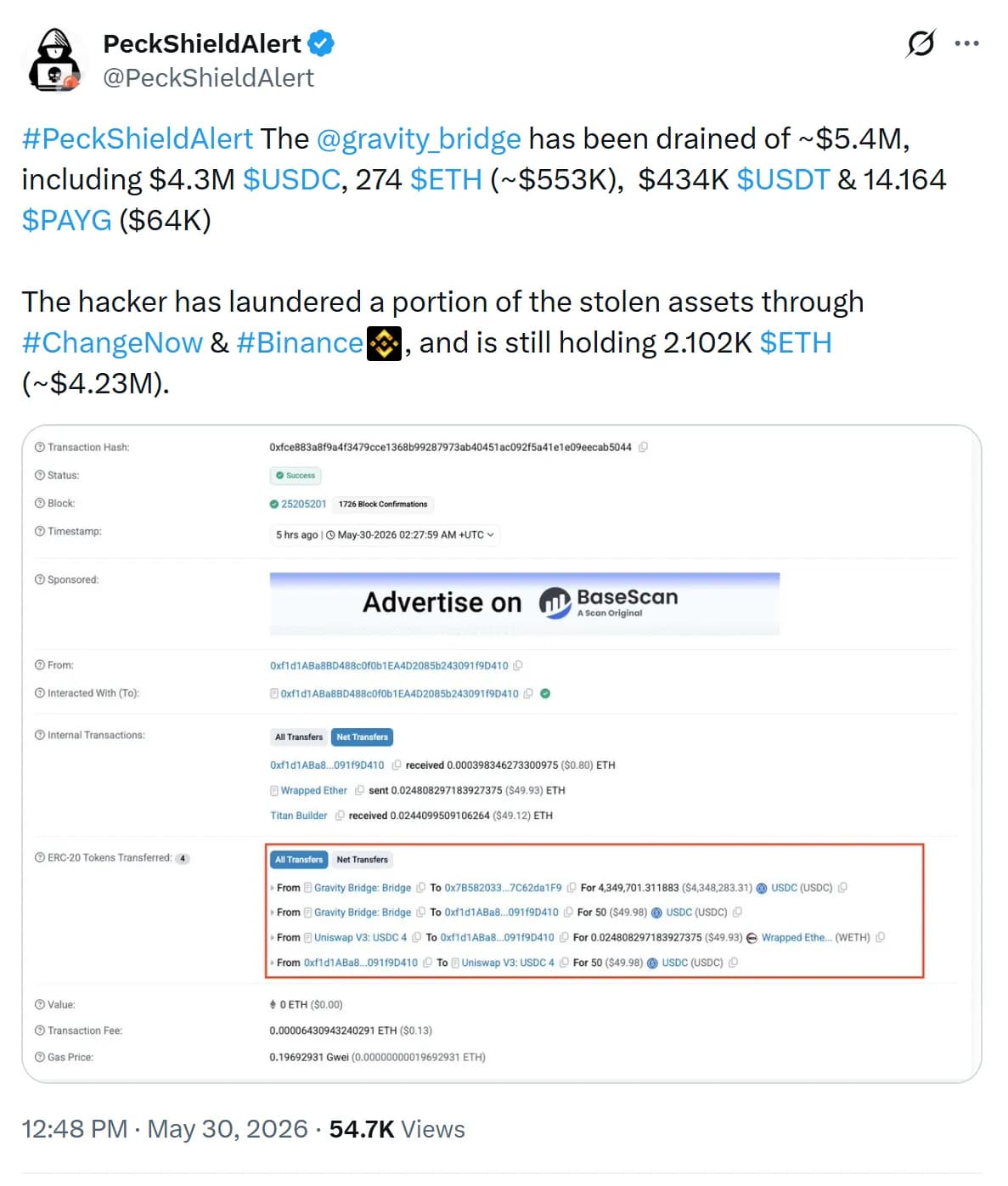
Gravity Bridge Hit by $5.4M Exploit as Bitcoin ETFs Bleed $2.97B Amid Peak Sentiment
Crypto News Gravity Bridge, a cross-chain protocol moving assets between Ethereum and the Cosmos ecosystem, was drained of roughly $5.4 million in a fresh exploit that has forced validators to suspend operations. On-chain analysts spotted suspicious outflows late Saturday, with early for

April Hits 4-Year DeFi Hack Record as SEC Charges $12.3M AI Bot Fraud
Crypto News Legacy financial institutions preparing to migrate trillions of dollars of assets onchain are stalling over an escalating security crisis, according to comments from CertiK chief executive Ronghui Gu. He framed the obstacle bluntly: bankers want the efficiency of decentralize
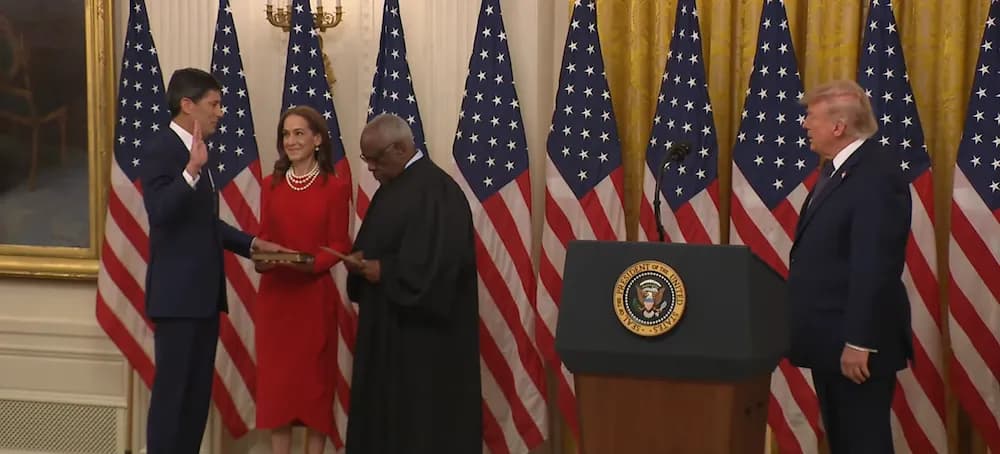
Warsh Sworn In as Fed Chair With 0% Rate Cut Odds, Polymarket Hit by $600K Exploit
Crypto News Kevin Warsh was officially sworn in as the new chairman of the United States Federal Reserve on Friday, ushering in a leadership change at the world's most influential central bank at a delicate moment for risk assets. At the swearing-in ceremony, President Donald Trump empha

Polymarket Hit by $520K Exploit and House Probe; Binance Disputes Iran Report
Crypto News The House Oversight Committee opened a formal investigation Friday into prediction-market giants Kalshi and Polymarket, citing concerns over insider trading and wagers placed on classified military activity. Committee Chair James Comer demanded documents covering know-your-cu
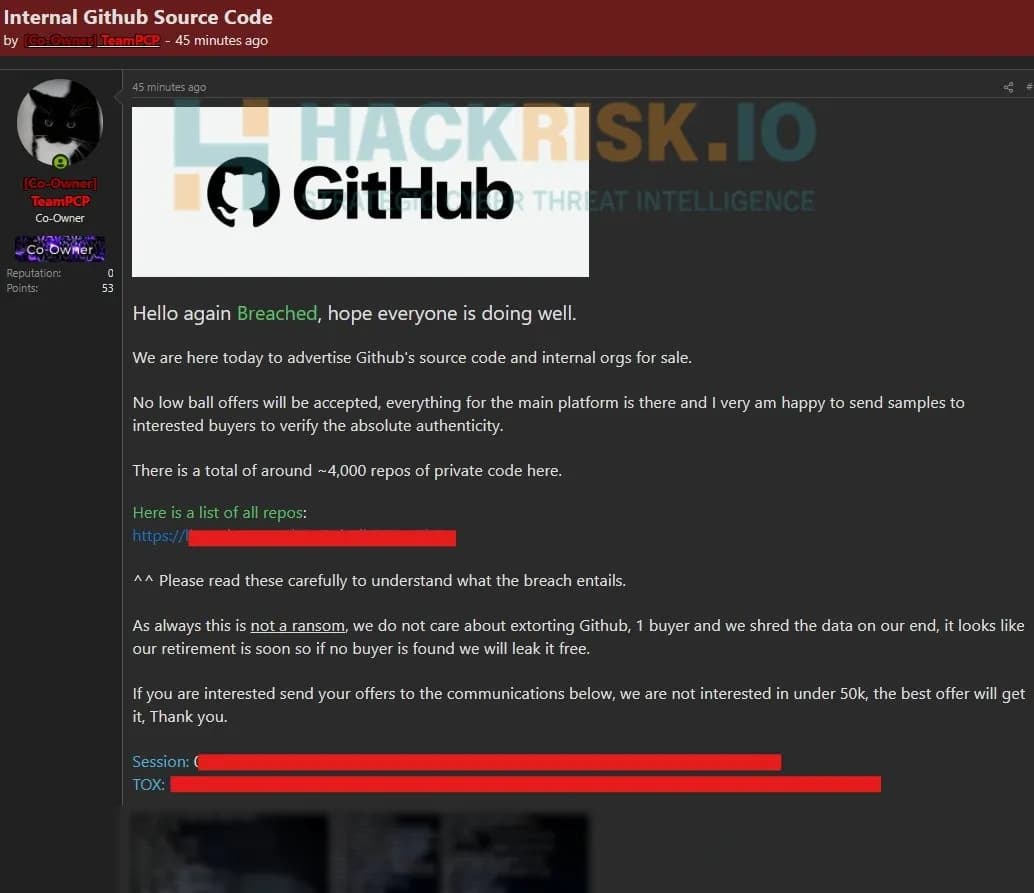
GitHub Confirms Repo Breach via VS Code Extension as Ark Adds $4.4M Bullish
Crypto News GitHub disclosed on Wednesday that it is investigating unauthorized access to its internal repositories after an employee device was compromised through a poisoned Visual Studio Code extension. The platform said it detected and contained the intrusion on Tuesday, removing the

Bitcoin Holds $76.8K Near Tom Lee's Line as Echo Protocol Hit by $76M Exploit
Bitcoin News Echo Protocol, a Bitcoin liquidity aggregation and yield infrastructure layer, suffered an exploit on its Monad deployment after an attacker minted 1,000 unauthorized eBTC tokens worth roughly $76.7 million. The team con

Standard Chartered to Cut 7,000 Jobs, SEC Readies Tokenized Stock Rules, Echo BTCFi Hit by $867K Exploit
Crypto News Standard Chartered confirmed plans to eliminate more than 7,000 corporate function roles by 2030, representing over 15% of that workforce segment, as the UK-headquartered lender accelerates its rollout of artificial intelligence and automation. Chief executive Bill Winters fr

CLARITY Act Advances as Strategy Buys Back $1.5B Debt, THORChain Refunds $10M Exploit
Crypto News The US CLARITY Act is being framed as a potential catalyst for domestic blockchain innovation, with venture firm a16z arguing that regulatory clarity could ripple far beyond the crypto sector. The firm pointed to the G
Mythos AI Shakes Crypto Security: AAVE Reaction
Anthropic's Mythos AI model is questioning crypto security approaches. The model targeting inter-system weaknesses highlights AAVE's response to the Kelp DAO exploit: 301M$ in commitments were collected. Coinbase is listing MEGA, the sector is turning to AI simulations.
Crypto Billionaire's 5M£ Gift to Farage Scandal
Nigel Farage received a 5M£ gift from crypto billionaire Harborne. While record donations are flowing to Reform UK, the government is restricting crypto funds. Details of BTC investments and the political scandal.
Powell Stays at the Fed: BTC Impact
Fed Chair Powell may step down from the chairmanship but remains a governor. Interest rates steady at %3,5-3,75. Hawkish dissenters held back the market. BTC $78.465 (+%0,07), S1 $71.926 support strong. Resistance R1 $79.397. Fed uncertainty impacting crypto; $85K possible.
ZK Technical Analysis May 2, 2026: Weekly Strategy
ZK is consolidating at $0.02 with a weekly %4.59 rise, downtrend intact but short-term bullish above EMA20. The critical $0.02 breakout will determine the direction, BTC sideways caution for alts.
Wasabi Hack: 5M$ Loss on Blast and Technical Analysis
Over $5M stolen in Wasabi Protocol hack; networks including Blast affected. Hacker exploited admin key, assets like WETH-PEPE drained. BLAST technical: S1 $0.0005 strong support. DeFi security lessons and FAQ.
Wasabi Protocol Hack: $4.5M Loss and DeFi Lessons
Wasabi Protocol hacked for 4.55M$: Single admin key drained vaults via UUPS. DRIFT delisted after Drift-like heist. ETH $2307, strong support $2221. DeFi losses exceed 770M$; multisig mandatory. Revoke LP approvals!
North Korean Hackers: DRIFT and KelpDAO Heist
North Korean hackers stole 577M$ in Q1 2026: DRIFT (285M$) and KelpDAO (292M$) hacks. In-depth review with technical details, price analysis, and delisting news. DRIFT at $0.04, bearish trend. Solana ecosystem affected.
North Korea DRIFT Hack: 285M$ Heist Details
North Korean hackers hit DRIFT Protocol with a $285M heist. TRMLabs: 76% of 2026 losses are DPRK. Price fell -7.39% with Upbit/Bithumb delist. Technical analysis: Support $0.0389, Resistance $0.0402. Social engineering tactics threaten DeFi.
FOMC Holds Rates Steady: BTC 78K, Meta USDC Push
FOMC kept rates at 3.50-3.75%, Powell issued shock warnings. BTC recovered to 78K, Meta started USDC payments with Solana/Polygon. AI earnings hit record: AWS 37.59B$. Technical: RSI 61, R1 79K strong resistance. Market cautious.
North Korean Hackers Stole $285M from DRIFT
North Korean hackers stole 577M$ from DRIFT and Kelp DAO, 76% of the year's hacks. TRM Labs report details: Social engineering, nonce exploit. DRIFT delisted from Upbit/Bithumb. North Korea's share broke the 76% record. Defenses must evolve.
April Hack Frenzy: Record Losses for AAVE and DeFi
Record in April crypto hacks: 600M$+ loss, KelpDAO 292M$, Drift 280M$, AAVE bad debt crisis. DRIFT delisted, AAVE $92.18 downtrend. Technical levels and social engineering tactics analyzed. DeFi security is evolving.
Frequently Asked Questions
What is a crypto hack and how does it differ from a scam?
A crypto hack is a technical compromise in which an attacker exploits a vulnerability in code, infrastructure, or key management to seize digital assets without the owner's consent. Typical vectors include smart-contract bugs (reentrancy, integer overflow, faulty access control), cross-chain bridge exploits, oracle manipulation, private-key leaks, and infrastructure breaches at centralized exchanges. A hack is fundamentally different from a scam: scams rely on social manipulation to convince victims to send funds voluntarily (rug pulls, phishing, fake giveaways), whereas a hack bypasses or breaks the security controls protecting funds the user never agreed to transfer. The distinction matters legally, because most jurisdictions treat unauthorized computer access and theft of digital property as separate criminal categories, and operationally, because the remediation path—on-chain tracing, exchange freezes, bounty negotiation with the attacker, or protocol-level fork—depends on which category the incident falls under.
How do hackers steal cryptocurrency from exchanges and DeFi protocols?
Attackers use a layered toolkit that varies by target. Against centralized exchanges, the most common entry points are compromised employee credentials, malicious insiders, vulnerable hot-wallet infrastructure, and supply-chain attacks against third-party software dependencies. Against DeFi protocols, attackers typically audit the publicly verifiable smart-contract source code for logic flaws such as flash-loan-assisted price manipulation, broken access control on admin functions, missing slippage checks, or unsafe delegatecall patterns. Cross-chain bridges remain the highest-value targets because they aggregate large reserves while relying on off-chain validator sets whose signing keys can be compromised. Once funds are extracted, attackers usually route the proceeds through mixing services, privacy chains, or decentralized exchanges to obscure the trail before attempting to off-ramp through smaller centralized venues with weaker KYC enforcement.
Can stolen cryptocurrency be recovered after a hack?
Recovery is possible but far from guaranteed and depends on how quickly the trail is identified and which venues the funds pass through. Public blockchains are transparent, so on-chain forensics firms can usually map the laundering path within hours, and if the attacker sends funds to a compliant centralized exchange, that exchange can freeze the deposit at the request of the victim, law enforcement, or the affected protocol. Many DeFi teams offer white-hat bounties—typically 5 to 20 percent of the stolen amount—in exchange for the return of the remainder, and a meaningful share of high-profile hacks ultimately resolve through such negotiations. Recovery becomes substantially harder when funds reach privacy mixers, cross-chain bridges to less transparent ledgers, or peer-to-peer over-the-counter markets. Statistically, only a minority of stolen crypto is fully recovered, which is why proactive security hygiene matters far more than post-incident pursuit.
Are crypto exchanges insured against hacks, and what happens to user funds?
Insurance coverage varies dramatically by jurisdiction and operator. Some large regulated exchanges maintain commercial crime insurance policies that cover a portion of hot-wallet losses, and several have built internal reserve funds—such as Binance's SAFU or Coinbase's customer protection pool—funded by trading fees and earmarked for breach reimbursement. However, these arrangements are voluntary, not equivalent to bank deposit insurance, and typically exclude losses caused by user-side compromise such as phishing or weak passwords. In a major hack, the exchange's response usually follows one of three paths: full reimbursement from reserves, socialized losses distributed across all users (the "haircut" model), or bankruptcy proceedings in which creditors recover cents on the dollar over multiple years. Users holding assets on an exchange should review the venue's published proof-of-reserves, audited financials, and explicit insurance terms rather than assume any default safety net applies.
How can I protect my cryptocurrency from being hacked?
Effective self-custody security rests on five practical layers. First, store the majority of long-term holdings in a hardware wallet or cold wallet that never connects to internet-facing software, and verify recipient addresses on the device screen rather than on the host computer. Second, separate operational wallets used for daily DeFi activity from savings wallets, so a compromised browser session cannot drain the entire balance. Third, audit every smart-contract token approval you have ever granted using a revocation tool, because dormant unlimited approvals to deprecated protocols are one of the largest sources of preventable losses. Fourth, treat your seed phrase as the single most valuable asset you own: never type it into any website, never photograph it, and store backups in physically separated, tamper-evident locations. Fifth, slow down: most successful retail hacks rely on urgency-driven phishing emails, fake support direct messages, or malicious browser extensions, and a 30-second pause to verify the source through an independent channel defeats the majority of attacks.